WRLD Tech Official Blog
Technology News + Reviews
A place where we share, review, and write about all things technology & design. Occasionally, company announcements too.
Subscribe now
Our newsletter delivered directly to your mailbox.
Industry News & Blog
- All
- AI for Business
- Awards
- Business
- Business Continuity
- Cloud
- Cybersecurity
- IT Management
- Microsoft
- New Technology
- News
- Opinion
- Productivity
- Space
- Trends
All
- All
- AI for Business
- Awards
- Business
- Business Continuity
- Cloud
- Cybersecurity
- IT Management
- Microsoft
- New Technology
- News
- Opinion
- Productivity
- Space
- Trends
BusinessCybersecurity
6 Reasons Access Management Has Become a Critical Part of Cybersecurity
Cybersecurity has become paramount for businesses and individuals alike. Cyber threats abound, and data breaches and malware attacks are costly. Attacks come from all sectors, including the cloud tools you use every day. The average employee uses 36 cloud-based services daily. Managing ...
September 5, 2023
Continue Reading →
Cybersecurity
What is Zero-Click Malware? How Do You Fight It?
In today’s digital landscape, cybersecurity threats continue to evolve. They pose significant risks to individuals and organizations alike. One such threat gaining prominence is zero-click malware. This insidious form of malware requires no user interaction. It can silently compromise devices and networks. ...
August 31, 2023
Continue Reading →
Cybersecurity
Top 7 Cybersecurity Risks of Remote Work & How to Address Them
Remote work has become increasingly popular in recent times. It provides flexibility and convenience for employees. Additionally, telecommuting reduces office costs for employers. Many also cite productivity benefits due to fewer distractions. Research shows a 56% reduction in unproductive time when working ...
August 25, 2023
Continue Reading →
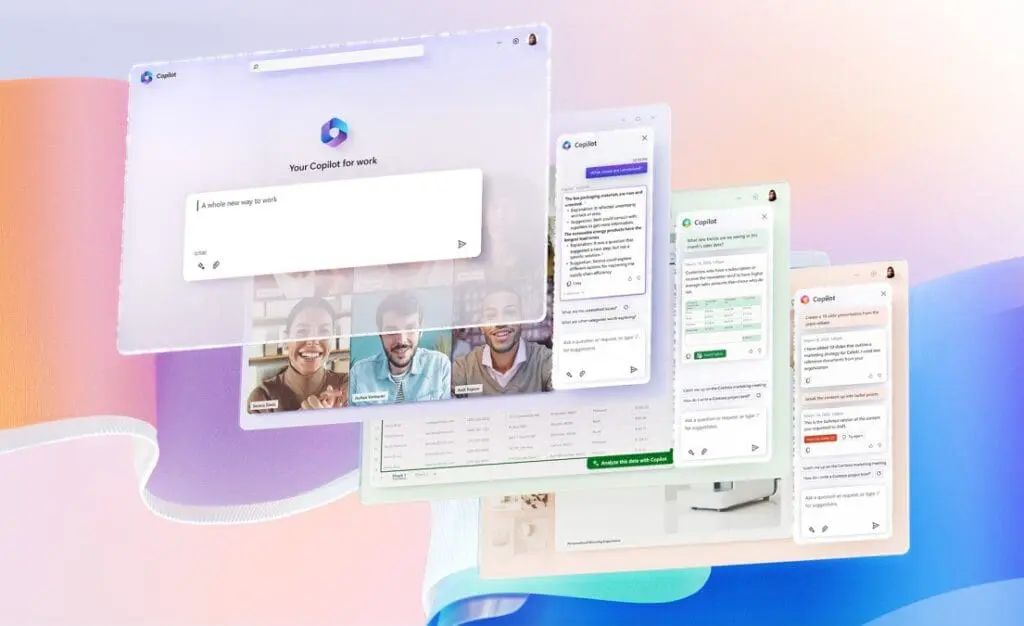
IT ManagementMicrosoftProductivity
Have You Tried Microsoft Universal Print? (Learn What It Can Do for You)
In today’s digital workplace, printing remains an essential function. This is true for just about all businesses. But keeping up with your print infrastructure can be a time-consuming task. One printer down can mean work comes to a standstill. Another issue is ...
August 20, 2023
Continue Reading →
IT ManagementOpinion
Do You Still Believe in These Common Tech Myths?
In today’s digital age, technology plays a significant role in our lives. But along with the rapid advancements and innovations, several myths have persisted. Is it okay to leave your smartphone charging overnight? Do Macs get viruses? And what about those 5G ...
August 10, 2023
Continue Reading →
AI for BusinessBusinessIT Management
Learn How Microsoft 365 Copilot Is Going to Transform M365 Apps
Advanced AI is a new buzzword in cloud computing. The launch of tools like ChatGPT and Bard have made big waves. Developers are now racing to introduce the next level of features to apps. Features that do part of your work for ...
July 31, 2023
Continue Reading →
BusinessCybersecurityIT Management
Business Email Compromise Jumped 81% Last Year! Learn How to Fight It
In recent years, electronic mail (email for short) has become an essential part of our daily lives. Many people use it for various purposes, including business transactions. With the increasing dependence on digital technology, cybercrime has grown. A significant cyber threat facing ...
July 15, 2023
Continue Reading →
BusinessBusiness Continuity
10 Tips to Help Small Businesses Get Ready for the Unexpected
What would you do if your business suffered a ransomware attack tomorrow? Do you have a contingency plan in case of a tornado, hurricane, or earthquake? The unexpected can happen anytime, and small businesses can get hit particularly hard. Small businesses are ...
July 10, 2023
Continue Reading →
Cybersecurity
9 NSA Best Practices for Securing Your Home Network
In today’s world, technology is ubiquitous, and connectivity is a must. Securing your home network has become more critical than ever. A secure home network is essential for protecting your personal data from hackers. From phishing to smishing (SMS phishing), it’s getting ...
July 5, 2023
Continue Reading →
CybersecurityIT Management
What Is Push-Bombing & How Can You Prevent It?
Cloud account takeover has become a major problem for organizations. Think about how much work your company does that requires a username and password. Employees end up having to log into many different systems or cloud apps. Hackers use various methods to ...
June 30, 2023
Continue Reading →
‘Keep my word’ is such a strange expression. At first glance, it just means ‘Be true to what you agreed on. But it could also mean, ‘Hold your words back.’ Keep them in. Let your actions speak instead.”
Peter Gould