Small businesses face many challenges, but technology can offer solutions. Digital tools can help small business owners simplify operations, increase efficiency, and enhance productivity.
There are many tools available, from innovative software to cutting-edge hardware. The right technology can give small business owners a competitive edge.
However, finding the best options can be daunting. Buying apps just because someone recommended them may not work for you. You need to identify your needs and optimize your solutions.
What are the main obstacles that SMBs encounter with cloud use? According to the 2023 State of the Cloud Report, they are cost management and security. The report also revealed that 47% of SMBs lacked resources and expertise.
We can assist you in selecting the best tech for growth and ROI. Let’s start by looking at some game-changing technologies. These tools can transform the way you run your small business.
Revolutionary Tech Tools for Small Business Owners
Searching for ways to streamline processes, improve communication, or elevate customer satisfaction? Look right here for a range of technology tools designed specifically for SMBs. These solutions possess the power to revolutionize your business’s triumph.
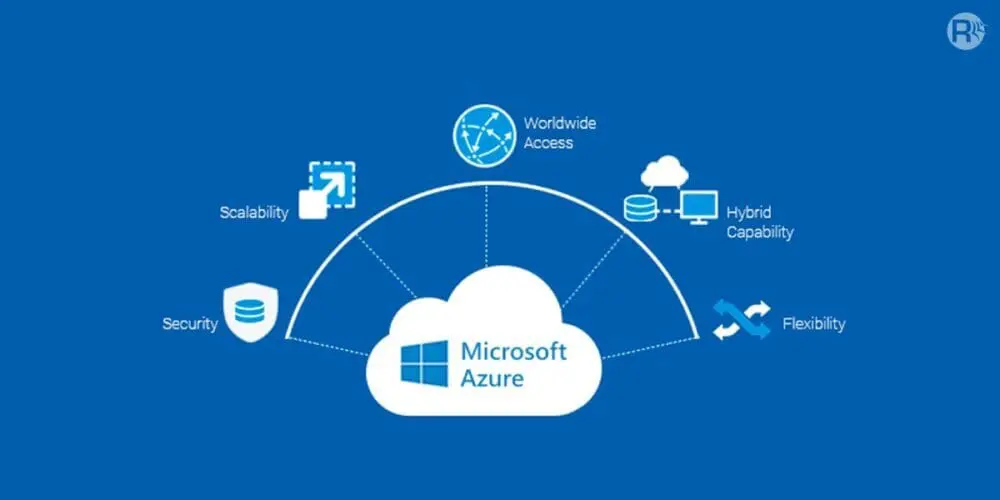
How Cloud Computing Enables Scalability and Flexibility
Cloud computing enables businesses to store, access, and manage their data more efficiently. Small businesses can benefit from apps like Microsoft 365 and Google Workspace, which offer enterprise-class features that were previously exclusive to large companies.
Microsoft Azure and Amazon Web Services (AWS) are examples of other cloud-based solutions. They offer scalable and flexible computing power to small business owners, who do not need to invest in expensive on-premises infrastructure.
Some of the advantages of cloud computing are:
- Enhanced collaboration
- Smooth data backup and recovery
- Increased accessibility
These features allow you and your team to work from any location and at any time. You can use the cloud to run your entire office, including your phone system, document storage, accounting, customer management, and more. The cloud offers cost-efficient solutions for small businesses of all kinds.
Customer Relationship Management (CRM) Software

CRM software is essential for delivering outstanding customer service in today’s competitive market. CRM platforms such as Salesforce and HubSpot help you centralize customer data and track interactions more effectively. You can also manage customer relationships better with CRM software.
Spreadsheets have their limitations. They require a lot of manual work and are prone to errors. They also lack collaboration features and can cause miscommunication or missed opportunities.
CRM software can enhance your sales process, marketing campaigns and customer support. You can learn more about your customers’ needs and preferences and customize your offerings accordingly. This will boost customer satisfaction and loyalty.
Tools for Smooth and Effective Teamwork

Small businesses need efficient collaboration, especially when their employees work in different locations or remotely. Collaboration tools such as Slack, Microsoft Teams, and Google Workspace enable this. They offer real-time communication, file sharing, and project management solutions.
These platforms unite teams and allow for smooth collaboration, effective task assignment, and streamlined workflows. The apps have features like chat, video conferencing, and document collaboration. These tools keep your team connected and productive, no matter where they are.
E-commerce Platforms for Online Sales
Small businesses can benefit from the growth of e-commerce. They can access more customers and generate more income. They can use platforms like Shopify, WooCommerce, and BigCommerce to build and run their online stores.
These platforms have everything a small business needs to succeed online. They have flexible designs, safe payment options, and easy inventory control. These features help small businesses create a strong online brand. They can offer products or services to customers anywhere.
Using Data Analytics to Make Better Decisions

Data analytics tools are valuable for any business. They can provide insights that inform decision-making. Small business owners can use platforms like Google Analytics and Microsoft Power BI to collect, analyze, and visualize data from various sources.
With data analytics, you can track website traffic, customer behavior, and sales trends. You can also identify opportunities, optimize marketing strategies, and make data-driven decisions. Data insights can help you grow your business.
Data analytics gives small business owners the power to understand their target audience. It also helps them spot areas for improvement quickly. They can then make smarter business choices.
Ask Us About Our Cloud Support to Boost Your Bottom Line
Technology can transform your small business by making your processes faster, your customers happier, and your efficiency higher. But it can be hard to figure out how to use it effectively. You don’t have to do it by yourself.
Let us help.
Give us a call today to schedule a chat about optimizing your cloud efficiency and costs.